The psychology behind ‘revenge travel’ dictates that travelers are going to start surging back this summer once the vaccine allows us to reach some semblance of herd immunity and guest confidence is restored. An issue therein is that the demand for a contactless hotel experience will remain, both due to safety concerns and a more general adjustment to it as part of the new normal.
The psychology behind ‘revenge travel’ dictates that travelers are going to start surging back this summer once the vaccine allows us to reach some semblance of herd immunity and guest confidence is restored. An issue therein is that the demand for a contactless hotel experience will remain, both due to safety concerns and a more general adjustment to it as part of the new normal.
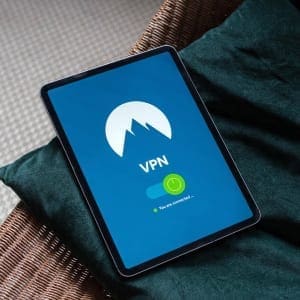
This means, though, that you must tighten the grip on tech stack in order to properly facilitate a contactless journey while not leaving any holes open for hackers. Indeed, cybersecurity – that is, the potential for data breaches or fraudulent activities by external persons or even by staff members – may be the next big issue for our industry once COVID-19 is behind us.
All told, this is a clear-cut matter of risk management in that a breach can besmirch a hotel brand’s reputation for many years to come. Or on a more micro-level, just imagine the damage if it was discovered (and made public) that, when using an electronic document platform for handling credit card payments, staff members were able to see a guest’s full credit card details while transferring them into the PMS and someone on your team was then illegally using that information.
But that’s what the IT department is here for, right? Yes and no. Your technology team is there to identify needs, maintain system integrities and remedy problems as they occur, but if the executive committee doesn’t have a firm grasp on some of the processes that enable these technologies to exist then there won’t be a viable strategic vision to guide these specialists. Cybersecurity, even down to the minutia of ensuring your own team never sees a full credit card, must be ingrained into upper management’s plans.
Because, when it comes to breaches, don’t say it won’t happen. It’s not an ‘if’ but a ‘when’. Beyond the more newsworthy, fast-acting malware, just think of all the unique IP addresses for every single node or repeater on premises and how a single vulnerability might be exploited to gain visibility on a wide range of sensitive data over a long period of time.
Indeed, there have already been a few successful cyberattacks that have resulted in major damages for leading hotel chains. Now, though, with our post-pandemic dependence on mobile apps and IoT-enabled devices for practically every significant point of interaction in the guest experience, the risk of a breach only becomes amplified as we continue to add to our tech stacks.
The end goal of a breach for a hacker, phisher or fraudster is money. They are looking for ways to cheat a property or individual from their possessions, or to impersonate someone as a means of unlawfully confiscating goods or cash. Certainly, the latest version of your PMS has layers of security to protect your guests’ identities housed within their data stores, but it still doesn’t hurt to reach out to them so that they can audit your systems and offer advice on mitigating any vulnerabilities.
Even better would be to hire an external consultant specializing in data security to perform a comprehensive audit of your entire tech stack. You never know what they may uncover. Particularly with so many new platforms and devices set up hastily during the early stages of Covid, perhaps there were some weaknesses that weren’t adequately addressed given the intense pressure we were all under to react on the spot.
Instead of a massive and systemic breach, however, the more common possibility comes from people falsifying credit card information. Although these may take place on a much smaller scale then, say, a man-in-a-middle attack where the hacker imitates a WiFi login portal then gains access and scrapes an entire guest database, they are still a nuisance to manage.
Foremost is mitigating the reputational damage. People who have had fraudulent charges put on their cards won’t exactly have the best impression of your hotel, regardless of your property’s culpability. Hence, you need systems and protocols in place to prevent fraud from occurring as well as deal with any fallout that may crop up on third-party review sites.
Next is chargebacks which are becoming all but unavoidable for what’s called ‘card not present’ transaction. For reference, these are in contrast to ‘Chip and PIN’ or ‘Chip and Signature’ transactions where there is some form of in-the-moment two factor authentication (2FA) to confirm that the person using the credit card is who they say they are. The problem with the chip-and-PIN or chip-and-signature methods is that they require some form of direct contact between the customer and an employee. At present, this isn’t contactless and comes with the risk of Covid spread. Hence, lodging merchant terminals (that’s us) are increasingly resorting to card-not-present payments where fraud and chargeback disputes are both significantly higher in likelihood.
Coming out of the last economic crisis just over a decade ago, there was a big push for all senior executives to learn the basics of revenue management, so much so that nowadays RM, yield management and dynamic pricing are everyday aspects of the life of a hotelier. Today the same knowledge adoption has just happened for all matters related to viral safety through the understanding of such terms as disinfection, sanitization, social distancing, electrostatic sprayers, PPE, cleanliness theater, occupancy buffers and fomite transmission.
The next normal of Q3/Q4 2021 will necessitate the same degree of comprehension for cybersecurity in order to protect guests, staff and the hotel organization from damages and to effectively guide any new technology deployments. Take some time to mandate some instruction in this field so that every associate or manager knows what’s at stake.